Recommended By





Latest News & Updates
The Only Plugin You Need For Login Protection

SMBs
- Protect against cyber threats and unauthorized access attempts
- Install and activate within minutes
- Affordable solution for robust website protection
- Focus on business growth while knowing your website is secure

Agencies
- Safeguard clients' websites from unauthorized access and potential data breaches
- Enhance agency reputation by providing robust website security services to clients
- Simplify security management across multiple client websites within a single platform
- Easily scale security services to accommodate growing agency clientele without compromising efficiency or effectiveness

Web Hosts
- Inspire confidence by offering reliable and secure hosting solutions
- Set apart hosting services with built-in comprehensive website protection
- Reduce customer churn by proactively protecting websites and mitigating security risks
- Add value and ancillary revenue by including advanced security features with hosting packages
Hundreds of Agencies Across The World Use LLAR






Frequently asked questions
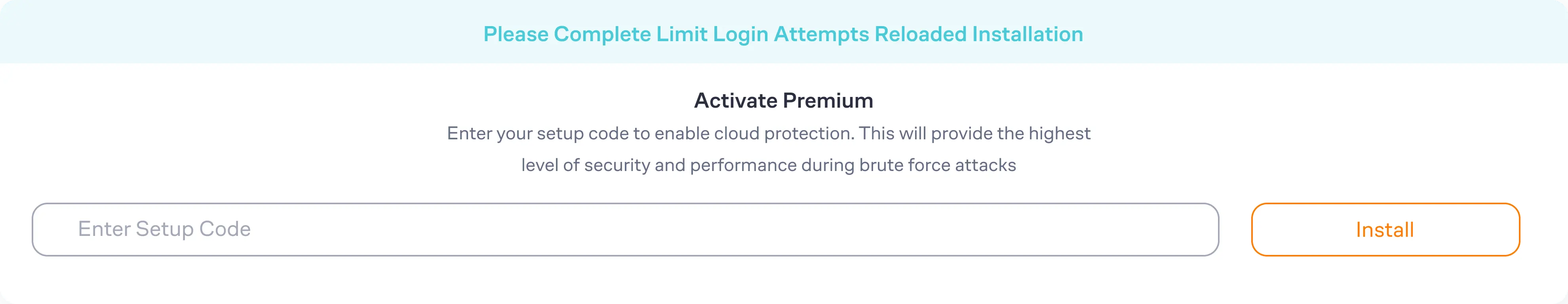
The software implements various techniques such as intelligent pattern recognition, rate limiting, and account lockouts to identify and mitigate brute force attacks. It detects repetitive login attempts, sets limits on login rates, and can temporarily suspend or lockout accounts after a certain number of failed login attempts.
Yes, the software offers customizable lockout settings. Administrators can define specific thresholds for failed login attempts and adjust the duration of lockouts according to their security requirements. This flexibility allows tailoring the protection measures to align with specific needs.
Yes, the software offers real-time alerts and notifications. These notifications can be sent via email instantly notifying administrators about detected security events, such as suspicious login attempts or lockouts. This enables prompt response and proactive management of potential threats.
Premium users receive advanced technical support via email. Free users have access to the WordPress community support forum.
In addition to brute force protection, the software provides a range of supplementary security measures. These can include IP denying and safelisting, intrusion detection systems (IDS), enhanced logging and reporting capabilities, and network synchronization. These additional features enhance overall website security and defense against various threats.