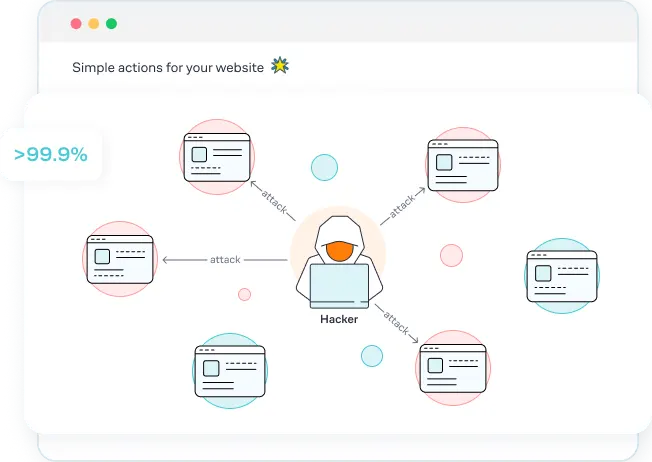
If you made it here, you’re probably wondering why you’re receiving several failed login attempt notifications in your WordPress dashboard and inbox. For most of you, this means that you are under something called a brute force attack. A brute force attack is when a cyber criminal tries to guess your website username and password in a highly repetitive process while often using sophisticated programs to do so. These attacks are the second most common threat to website owners - Faulty plugins and themes are #1.
Brute force attacks are popular with cyber criminals because they are simple and reliable. They often let the computers do the work by trying hundreds of thousands of username and password combinations until they figure it out. The best way to fight back against the attacks is to stop them in progress: If they make it through, it might be too late.
In this article we’ll address the following questions:
- How can I tell that I’m under attack?
- What did I do to expose myself to an attack?
- How do I better protect my website?
- What are the consequences if an attack is successful?
How can I validate if this is an actual brute force attack?
There are times when you’ll have friendly programs or users that will be the cause of failed login attempt notifications. An easy way to check if the attack is legitimate is to copy the IP address from the lockout notification, and go to https://whatismyipaddress.com/ip-lookup. Enter in the IP address to see if you recognize the location. If the location is not somewhere you recognize, then you are probably under an attack. You might notice dozens or hundreds of IPs each day.
What is considered a serious attack?
We consider any attack serious whether it’s a few attempts or thousands. Keep in mind that cyber criminals have advanced algorithms and machine learning capabilities to improve their chances at guessing every time they try. This means that they don’t need very many tries to break through, especially if your password is weak or being reused from other accounts. The more serious attacks will slow down your site to the point where your customers will have a difficult time using it. This can last for several minutes, hours, or days.
I think these attacks might be fake, what is going on?
Some users feel that it’s impossible to receive so many failed login attempts, especially since they’re site was just created or they have minimal human traffic. Let us be clear that these failed login attempts are NOT generated by the plugin. It might feel like these failed login attempts are fake, but there is an explanation to why this is happening.
New websites are often hosted on shared IP address, which make it very easy for hackers to find. Also, new domain names are often crawled once they are created, so as soon as a WordPress website is built on it, it’s vulnerable to attacks. New websites are often the best target since security is not top of mind for new site owners.
Why my website?
Greater than 99.9% of brute force attacks are chosen at random, so don’t waste any of your time trying to investigate. Cyber criminals will create programs that crawl the internet and choose their victims arbitrarily.